ECCelerate™ 6.4
Core Crypto Toolkits
The following tables list all pre-defined ECC domain parameters. Use the iaik.security.ec.common.ECStandardizedParameterFactory methods to make use of them. You can either provide the curve name (getParametersByName(name) method), use the object identifier (getParametersByOID(oid) method) or select domain parameters by the key length (getParametersByBitLength(bits) method). Some of the curves have more than one name. In this case you can specify any you like.
Supported ECC Domain Parameter for Elliptic Curves over Prime Fields
This is the recommended field type and more efficient in software. The NIST curves are being used if you initialize the keypair generator just with the keysize.
| key length | OID | X9.62 | NIST | SEC2 | RFC 5639 | ANSSI |
| 160 | 1.3.132.0.9 | secp160k1 | ||||
| 160 | 1.3.132.0.8 | P-160 | secp160r1 | |||
| 160 | 1.3.132.0.30 | secp160r2 | ||||
| 160 | 1.3.36.3.3.2.8.1.1.1 | brainpoolP160r1 | ||||
| 160 | 1.3.36.3.3.2.8.1.1.2 | brainpoolP160t1 | ||||
| 192 | 1.2.840.10045.3.1.1 | prime192v1 | P-192 | secp192r1 | ||
| 192 | 1.3.132.0.31 | secp192k1 | ||||
| 192 | 1.2.840.10045.3.1.2 | prime192v2 | ||||
| 192 | 1.2.840.10045.3.1.3 | prime192v3 | ||||
| 192 | 1.3.36.3.3.2.8.1.1.3 | brainpoolP192r1 | ||||
| 192 | 1.3.36.3.3.2.8.1.1.4 | brainpoolP192t1 | ||||
| 224 | 1.3.132.0.33 | P-224 | secp224r1 | |||
| 224 | 1.3.132.0.32 | secp224k1 | ||||
| 224 | 1.3.36.3.3.2.8.1.1.5 | brainpoolP224r1 | ||||
| 224 | 1.3.36.3.3.2.8.1.1.6 | brainpoolP224t1 | ||||
| 256 | 1.2.840.10045.3.1.7 | prime256v1 | P-256 | secp256r1 | ||
| 256 | 1.3.132.0.10 | secp256k1 | ||||
| 256 | 1.3.36.3.3.2.8.1.1.7 | brainpoolP256r1 | ||||
| 256 | 1.3.36.3.3.2.8.1.1.8 | brainpoolP256t1 | ||||
| 256 | 1.2.250.1.223.101.256.1 | FRP256v1 | ||||
| 320 | 1.3.36.3.3.2.8.1.1.9 | brainpoolP320r1 | ||||
| 320 | 1.3.36.3.3.2.8.1.1.10 | brainpoolP320t1 | ||||
| 384 | 1.3.132.0.34 | P-384 | secp384r1 | |||
| 384 | 1.3.36.3.3.2.8.1.1.11 | brainpoolP384r1 | ||||
| 384 | 1.3.36.3.3.2.8.1.1.12 | brainpoolP384t1 | ||||
| 512 | 1.3.36.3.3.2.8.1.1.13 | brainpoolP512r1 | ||||
| 512 | 1.3.36.3.3.2.8.1.1.14 | brainpoolP512t1 | ||||
| 521 | 1.3.132.0.35 | P-521 | secp521r1 | |||
Supported ECC Domain Parameter for Elliptic Curves over Binary Fields
We only support polynomial base representation of this field type.
| key length | OID | X9.62 | NIST | SEC2 |
| 163 | 1.3.132.0.1 | K-163 | sect163k1 | |
| 163 | 1.3.132.0.15 | B-163 | sect163r2 | |
| 163 | 1.3.132.0.2 | sect163r1 | ||
| 191 | 1.2.840.10045.3.0.5 | c2tnb191v1 | ||
| 191 | 1.2.840.10045.3.0.6 | c2tnb191v2 | ||
| 191 | 1.2.840.10045.3.0.7 | c2tnb191v3 | ||
| 193 | 1.3.132.0.24 | sect193r1 | ||
| 193 | 1.3.132.0.25 | sect193r2 | ||
| 233 | 1.3.132.0.26 | K-233 | sect233k1 | |
| 233 | 1.3.132.0.27 | B-233 | sect233r1 | |
| 239 | 1.3.132.0.3 | sect239k1 | ||
| 239 | 1.2.840.10045.3.0.11 | c2tnb239v1 | ||
| 239 | 1.2.840.10045.3.0.12 | c2tnb239v2 | ||
| 239 | 1.2.840.10045.3.0.13 | c2tnb239v3 | ||
| 359 | 1.2.840.10045.3.0.18 | c2tnb359v1 | ||
| 409 | 1.3.132.0.36 | K-409 | sect409k1 | |
| 409 | 1.3.132.0.37 | B-409 | sect409r1 | |
| 431 | 1.2.840.10045.3.0.20 | c2tnb431r1 | ||
| 571 | 1.3.132.0.38 | K-571 | sect571k1 | |
| 571 | 1.3.132.0.39 | B-571 | sect571r1 | |
Supported twisted Edward curve domain parameters
ECCElerate supports twisted Edward curves via
iaik.security.ec.ec.EdStandardizedParameterFactory. You can either provide the curve name (
getParametersByName(name) method) or the object identifier (
getParametersByOID(oid) method). The instances named starting with
Curve are for use in the context of X25519 and X448. The instances named starting with
Edwards are for use in the context of EdDSA.
| Name | OID |
| Curve25519 | 1.3.101.110 |
| Curve448 | 1.3.101.111 |
| Edwards25519 | 1.3.101.112 |
| Edwards448 | 1.3.101.113 |
NIST SP-800-57a Part1 Document
| Bits of Security | Example Algorithm | Prime Field ||p|| * | Binary Field m |
| 112 | Triple-DES | 224 | 233 |
| 128 | AES-128 | 256 | 283 |
| 192 | AES-192 | 384 | 409 |
| 256 | AES-256 | 521 | 571 |
*) by ||p|| is meant the length of the binary expansion of the integer p.
The ECCelerate™ Add-On holds algorithms that are (assumed to be) subject to patent claims. In case you want to employ our arithmetical optimizations to gain full performance, you must include iaik_eccelerate_addon.jar into your classpath.
There have been many patents granted and applied for in the field of ECC. This means that this implementation may contain an implementation of an algorithm that is IPR-protected in some country. At this time we are not aware of a specific case, some arithmetical speedups (included in the separate iaik_eccelerate_addon.jar file). If anybody identifies a case of potential patent infringement, we would be grateful if you could inform us about this to enable us dealing with the issue.
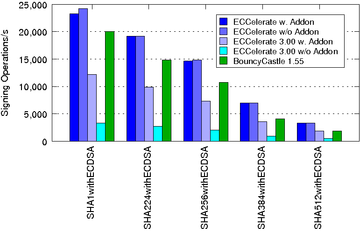
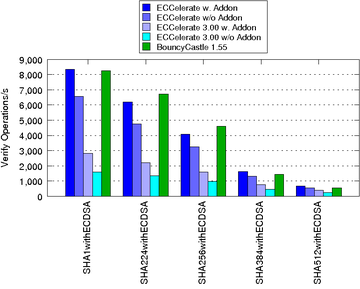
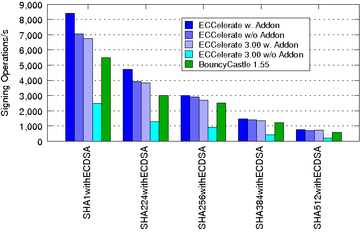
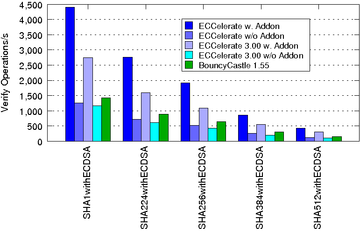
The subsequent charts show the performance improvements of ECCelerate™ with regard to our old IAIK-ECC library. In case of ECCelerate™ the default optimization level was used.
The performance was measured on an Intel(R) Core(TM) i7-4790 CPU @ 3.60GHz, 16GB DDR3 RAM running Ubuntu Linux 15.04/amd64 and JDK 1.7.0_80/amd64 in server mode.
| ECDSA Signing Operations/s using NIST Curves over Fp:
|
| ECDSA Verify Operations/s using NIST Curves over Fp:
|
| ECDSA Signing Operations/s using NIST Curves over F2m:
|
| ECDSA Verify Operations/s using NIST Curves over F2m:
|
For an introduction to the IAIK ECCelerate™ library please have a look at the following Tutorial
The JavaDoc™ API is also available online.
| Class or Package | Bug / Change / New Feature | Description and Examples |
|---|---|---|
| iaik.security.ec.common | B | Fixed leading zero encoding issue of curve parameters when using |
| iaik.security.ec.ssl | C | Removed iaik_eccelerate_ssl.jar as iSaSiLk now includes the neccessary dependencies. |
| Class or Package | Bug / Change / New Feature | Description and Examples |
|---|---|---|
| iaik.security.ec.ecdsa | C | ECDSA Signature verification now fails if Signature contains invalid DER encoding. |